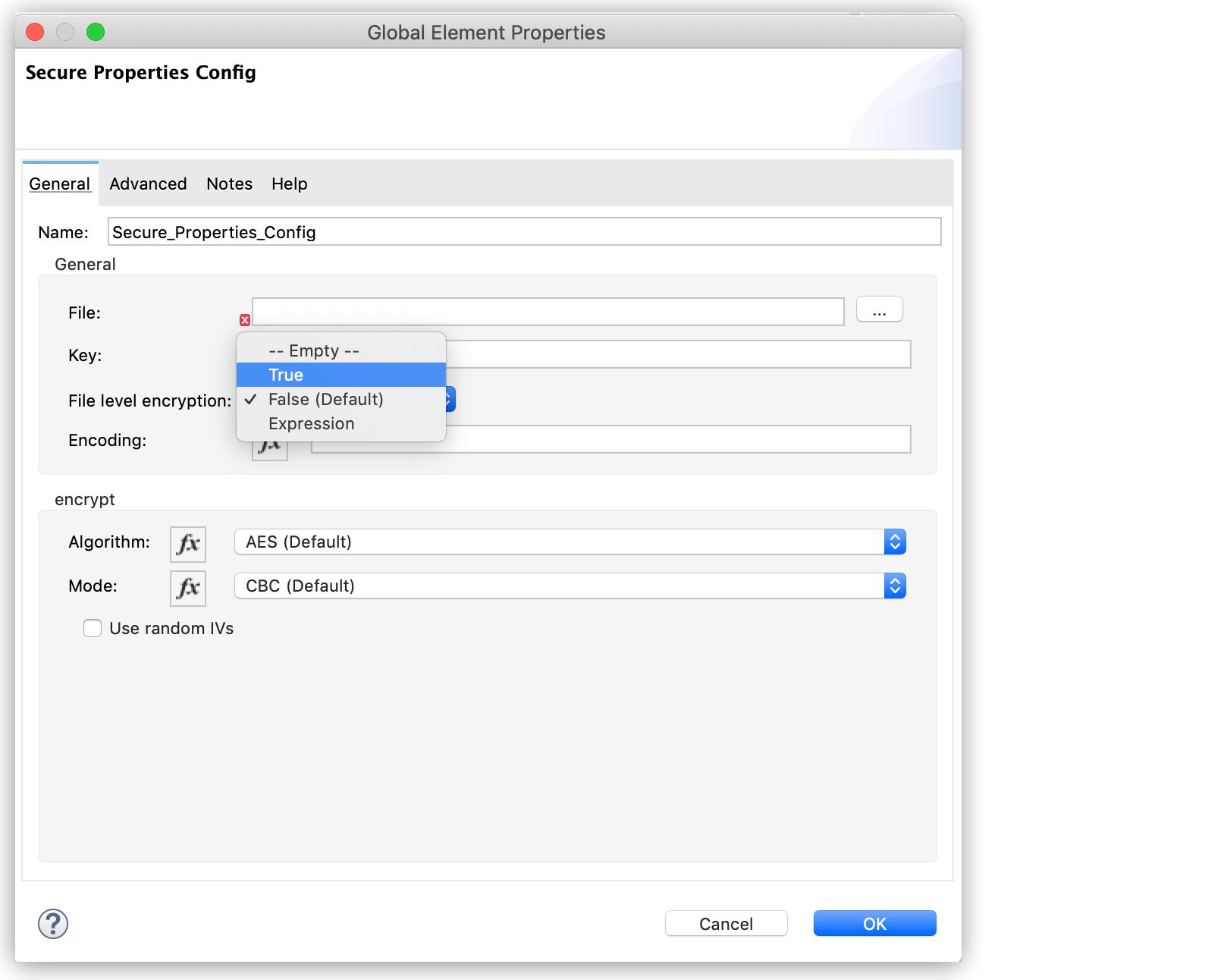
Key features include endpoint encryption hard drive and removable media email encryption file encryption on premises and in the cloud cloud centralized management key management.
Encryption key management tools.
Leveraging fips 140 2 compliant virtual or hardware appliances thales key management tools and solutions deliver high security to sensitive environments and centralize key management for your home grown encryption as well as your third party applications.
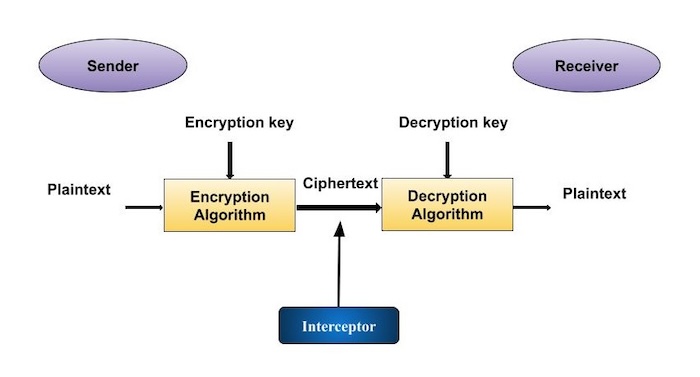
If the encryption and decryption processes are distributed the key manager has to ensure the secured distribution and management of keys.
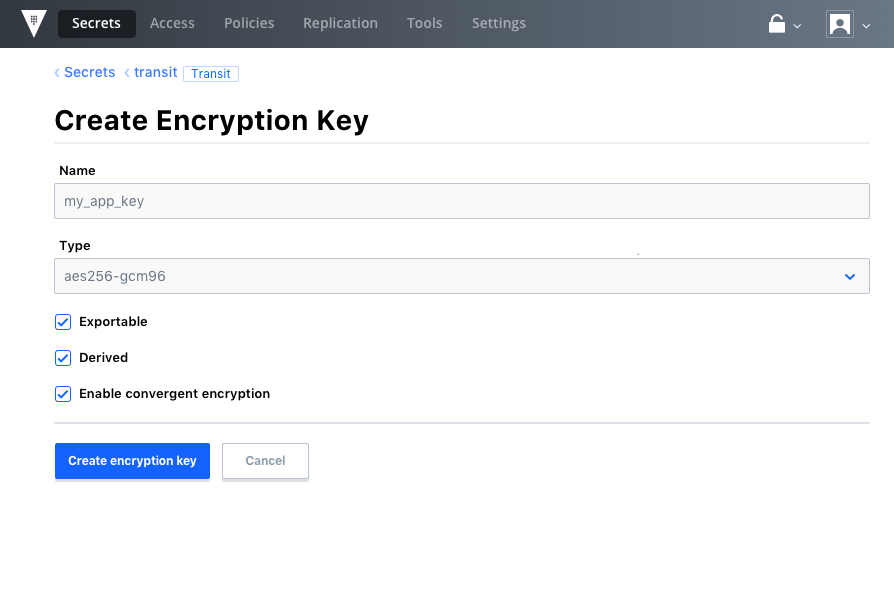
Key management application program interface km api.
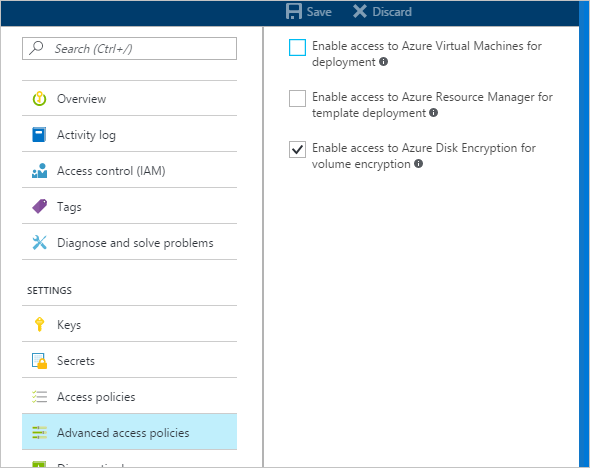
Hsm as a service is another option it provides a combination of cloud and hardware key management and storage.
This gives you greater command over your keys while increasing your data security.
In contrast to the complexity of learning and using a different key management tool for each cloud service provider you work with hsm as a service gives you simplicity without sacrificing security surely an encryption key management best practice.
Proper management will ensure encryption keys and therefore the encryption and decryption of their sensitive information are only accessible for approved parties.
Hsm devices use hardware interfaces with a server process as an intermediary between an application.
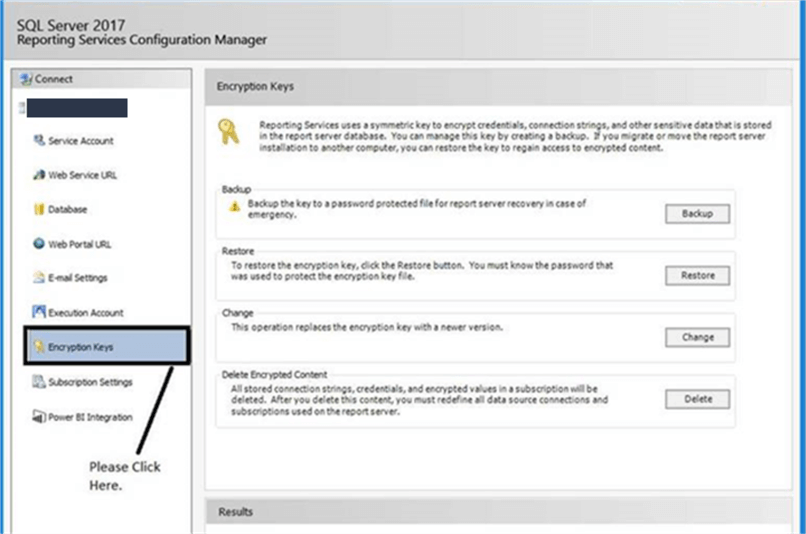
Key management software is available for the cloud but another common method of key management is the hardware security module hsm which stores encryption keys in a physical module.
An important consideration in selecting an encryption key management product is to ensure that keys when generated are constantly protected so that the master key is secure from a breach.
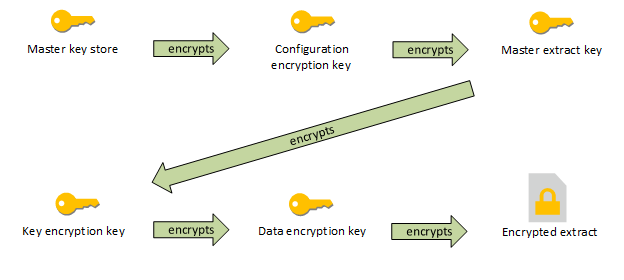
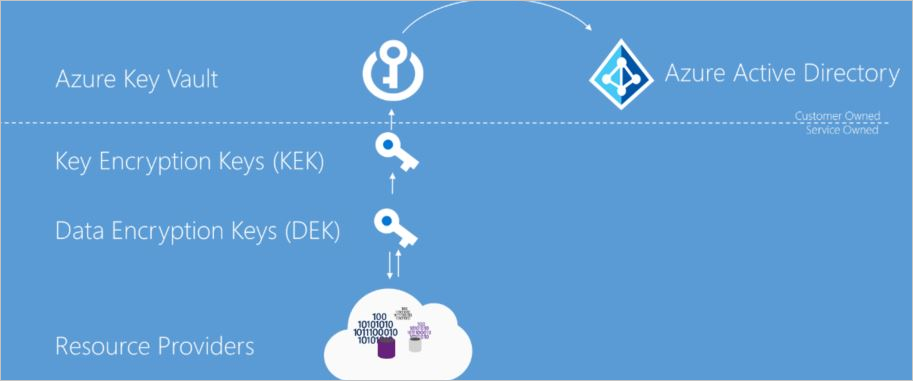
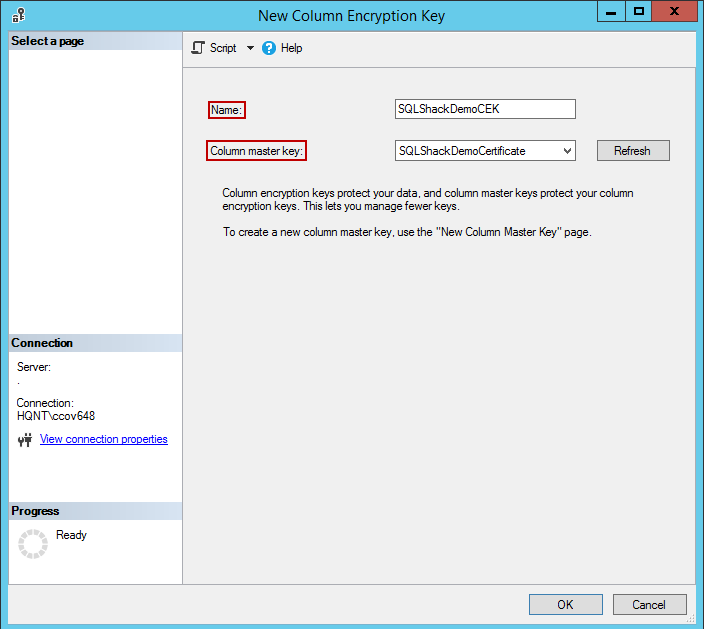
Is an encryption key whose function it is to encrypt and decrypt the dek.
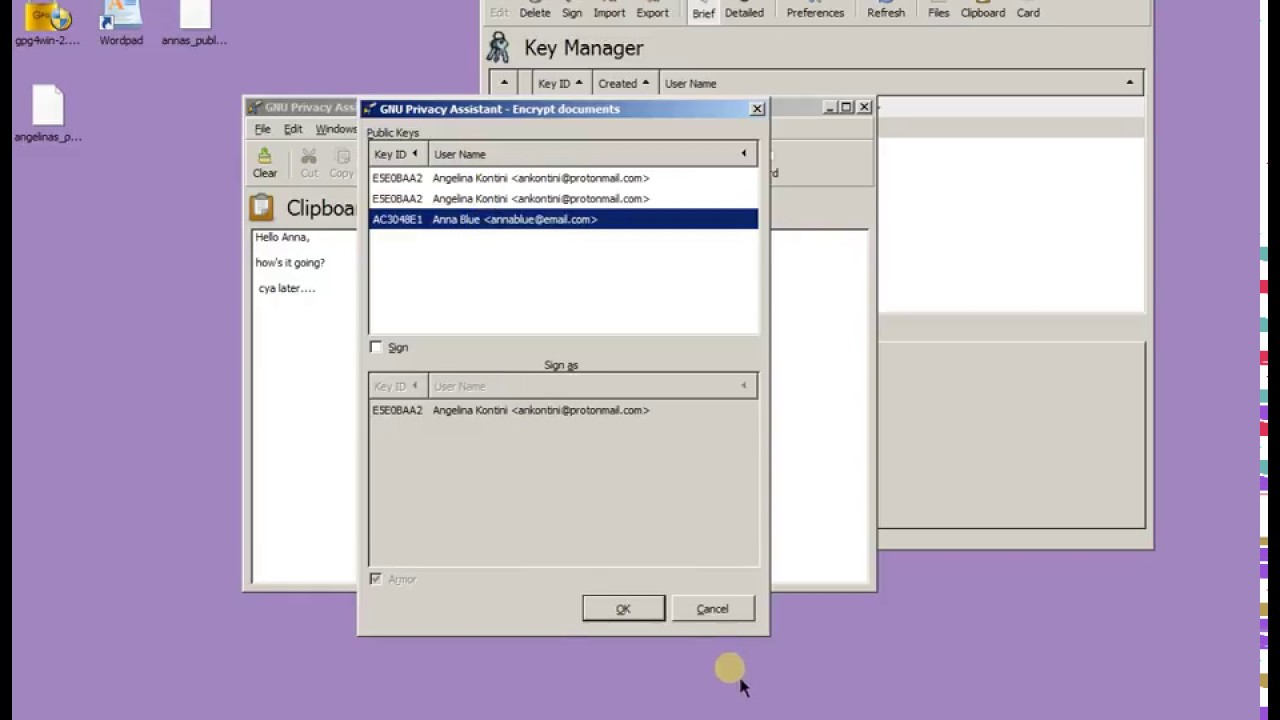
Is an application interface that is designed to securely retrieve and pass along encryption keys from a key management server to the client requesting the keys.
A number of vendors offer hsm for both key management and encryption acceleration.
One time use keys limit the exposure of data to theft the same way one time use credit card numbers limit the chance of funds being stolen.
Hsm devices store encryption keys on hardware or software modules.
Encryption key management best practices for multicloud environments.
Key encryption key kek.